Secure Zero Trust Networking Made Simple
Kensei gives small and midsized businesses a simple way to manage Zero Trust Network Access (ZTNA) for an identity-first secure setup on remote and internal devices. Reduce risk across your entire environment without a complex setup today.
What Is Kensei?
Kensei is a Zero Trust Network Access (ZTNA) and private mesh networking platform designed specifically for small and midsized businesses and replaces VPNs, scattered firewall rules, separate DNS tools, and manual access controls with one unified system.
It creates a private, identity-based network around your organization and controls access at the application level.
Instead of placing users onto your entire internal network, Kensei connects them only to the specific systems they are approved to use.
Access is built on three foundations:
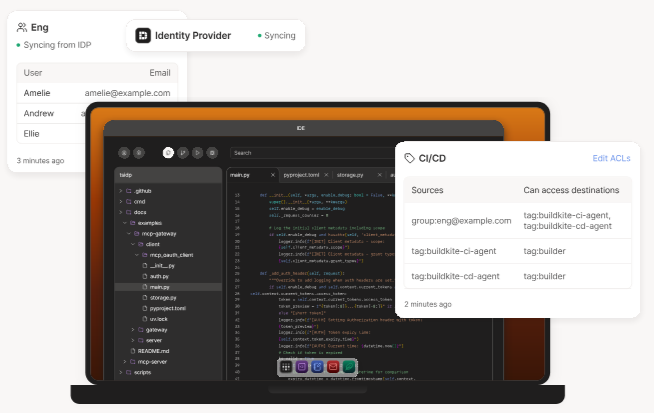
1. User Identity – Integrated with Okta, Google, Azure, and other SSO providers.
2. Device Trust – Only approved, secure devices are allowed to connect.
3. Defined Policy – Permission-based access to specific applications.
Every connection is verified. Every access decision is logged and auditable. All of this is managed from a clean, structured dashboard designed for clarity — not complexity.
Works seamlessly with your existing tools
Connect Kensei with your favorite platforms in minutes. Use our open API or ready-made integrations.
sourcetree
Accounting
Teams
Productivity
Mailchimp
Productivity
Zendesk
Productivity
Jira
Project Management
Zapier
Automation
Treehouse
Training
Visa
Payments
Stripe
Payments
PayPal
Payments
Square
Payments
Plaid
Bank Feeds
World pay
Payments
Sberbank
Payments
Alfa Bank
Payments
Yandex Kassa
Payments
Why Teams Use Kensei
A consistent access model.
As organizations scale, security becomes fragmented. Remote employees need access from anywhere. Cloud systems hold sensitive data. Internal tools must remain private. Contractors require limited access. Automation and AI now act under real user accounts. Most teams solve these problems by layering multiple tools together. Kensei replaces that patchwork with one consistent access model.
AI-Assisted Insights
Kensei's AI systems detect unusual access patterns, highlight policy gaps, and suggest improvements based on real usage, helping security teams respond faster and refine access controls with less manual review.
Reduce Operational Overhead
Link offices and environments into one secure private network while managing access policies centrally, eliminating scattered rules and applying changes instantly across systems.
Protect Cloud and SaaS Applications
Restrict access to email, ERP systems, repositories, and dashboards based on identity, device posture, and real-time threat signals — not just a password.
Connect Multi-Site Networks in Minutes
Add users, services, contractors, and locations without rebuilding your network architecture. Kensei connects offices, remote employees, and home networks into one secure mesh in minutes.
Simple Setup & Management
Deploy Kensei into established environments without replacing existing systems. Setup is straightforward, day-to-day management is centralized, and policies remain intuitive as your environment grows.
Secure Remote Work
Employees can safely access internal systems from anywhere without exposing your infrastructure. Access policies follow users and devices for strict control over sensitive systems.
How It Works
Easy Interface
Connect Identity
Integrate with Okta, Azure AD, or Google Workspace. Users sign in with the same credentials they use.
Define Access by Application
Choose exactly who can access which systems. Users are not automatically added to your full network by default.
Enforce Device Trust
Require approved devices and defined security conditions before granting access. If credentials are compromised, attackers cannot connect from unknown machines.
Monitor and Expand
Centralized logs and audit visibility give you control as your business grows. Deploy alongside your existing infrastructure without redesigning your network.
Real-Time Visibility and AI-Assisted Monitoring
Kensei gives administrators live insight into:
- • Who is accessing what applications
- • Which domains are being blocked by K-DNS
- • Device trust status
- • Unusual behavior patterns
- • Policy enforcement in real time
With our visual network flow maps, we make it easy to see allowed and blocked connections across your entire environment. Admins receive structured alerts instead of raw logs, highlighting important events and reducing manual review time.
You are not just granting access — you are seeing it happen.
Built-In Threat Protection and Intelligence with
K-DNS
Kensei strengthens more than just access control… it also protects the connections themselves and adapts to modern workflows.
Every connection begins with DNS resolution. Kensei protects at that layer.
Blocks phishing, malware, and malicious domains
Stops threats before pages ever load, at the DNS resolution layer.
Stops ads and tracking domains at the DNS level
Consistent enforcement across all connected devices, without browser plugins.
Applies policies consistently across all connected devices
Fully integrated into your Zero Trust policies — not a standalone tool.
Integrated DNS Protection (K-DNS)
-
Blocks phishing, malware, and malicious domains
-
Stops ads and tracking domains at the DNS level
-
Prevents threats before pages load
-
Applies policies consistently across all connected devices
-
Provides real-time domain visibility for administrators
Unlike standalone DNS tools, K-DNS is fully integrated into your Zero Trust policies.
Prebuilt Compliance Profiles
Built for security-conscious SMBs, Kensei offers prebuilt compliance policy templates that you can finetune for your security needs.
Medical Practices
HIPAA-Aligned Controls
HIPAA requires strict access controls, audit logging, and safeguards against unauthorized access. Kensei helps medical practices enforce per-application Zero Trust access and log and retain access events for audit readiness.
CPA and Financial Offices
Secure client data, protect internal systems, maintain structured audit logs for regulatory review, and simplify compliance documentation… without needing a dedicated security team.
Insurance Agencies
Gain centralized visibility and consistent policy enforcement across distributed offices under Kensei's secure private mesh network, and keep confidential data secure and protected.
Legal Firms Handling Sensitive Data
Secure access for partners and staff without exposing your entire internal network. Kensei's legal profiles allows firms to manage confidential communications and records easily and securely.
Distributed & Remote Teams
Modern businesses often operate fully remote, using cloud platforms and developer environments without a traditional office network. Gain enterprise-grade access security and control from day one, without the complex setup.
How Kensei Compares
Traditional VPNs provide network connectivity.
Kensei provides Zero Trust Network Access (ZTNA) with built-in DNS protection and AI-assisted monitoring, safeguarding your data into a single unified platform.
Capability
Access Model
Device Enforcement
DNS Protection
AI Controls
Onboarding
Visibility
Traditional VPN
Broad network access
Limited
Separate tool
None
Technical setup
Limited logs
Kensei
Rated #1Per-application access
Built-in device trust
Integrated
Built-in safeguards
Guided and clear
Centralized audit logs
Enterprise-level control without enterprise-level complexity.
Get Started
Leave your name and email and we’ll be in touch shortly.